Security researchers have disclosed a security issue that could allow attackers to weaponize the VirusTotal platform as a conduit for remote code execution (RCE) on unpatched third-party sandboxed machines that use antivirus engines.
The vulnerability has now been patched to “remotely execute commands from within” [through] VirusTotal platform and gain access to its various scanning capabilities,” Cysource researchers Shai Alfasi and Marlon Fabiano da Silva said in a report shared exclusively with The Hacker News.

VirusTotal, part of Google’s Chronicle Security subsidiary, is a malware scanning service that analyzes suspicious files and URLs and checks for viruses with over 70 third-party antivirus products.
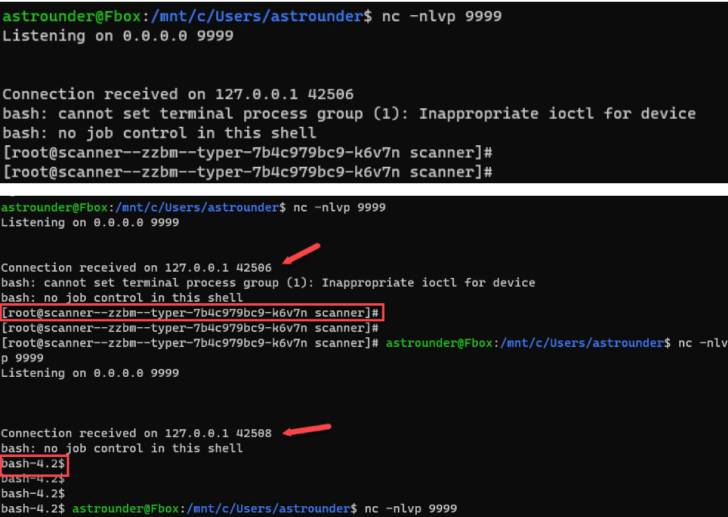
The attack method involves uploading a DjVu file through the platform’s web user interface, which, when passed to multiple third-party malware scanning engines, could trigger the exploitation of a high-severity remote code execution vulnerability in ExifTool, an open-source utility that uses For reading and editing EXIF metadata information in image and PDF files.
The high-severity vulnerability, tracked as CVE-2021-22204 (CVSS Score: 7.8), is a case of arbitrary code execution caused by ExifTool’s improper handling of DjVu files. The issue has been fixed by its maintainers in a security update released on April 13, 2021.
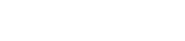
As a result of this exploit, it grants a reverse shell to affected machines that link to some antivirus engines that have not yet been patched for the remote code execution vulnerability, the researchers noted.
It’s important to note that the vulnerability does not affect VirusTotal, whose founder Bernardo Quintero confirmed in a statement shared with The Hacker News that this is expected behavior, and that code execution is not on the platform itself, but on a third party that analyzes and executes the samples. Scan the system. The company also said that the version of ExifTool it uses is not susceptible to the vulnerability.

Cysource said it responsibly reported the vulnerability through Google’s Vulnerability Rewards Program (VRP) on April 30, 2021, and immediately corrected the security flaw.
This is not the first time the ExifTool vulnerability has emerged as a conduit for remote code execution. Last year, GitLab fixed a critical vulnerability (CVE-2021-22205, CVSS Score: 10.0) related to improper validation of user-supplied images, resulting in arbitrary code execution.
renew: The story has been modified from VirusTotal’s statement to clarify the nature of the exploit.